Google Uncovers 'Initial Access Broker' Working with Conti Ransomware Gang
Google's Threat Analysis Group (TAG) took the wraps off a new initial access broker that it said is closely affiliated to a Russian cyber crime gang notorious for its Conti and Diavol ransomware operations.
Dubbed Exotic Lily, the financially motivated threat actor has been observed exploiting a now-patched critical flaw in the Microsoft Windows MSHTML platform (CVE-2021-40444) as part of widespread phishing campaigns that involved sending no fewer than 5,000 business proposal-themed emails a day to 650 targeted organizations globally.
"Initial access brokers are the opportunistic locksmiths of the security world, and it's a full-time job," TAG researchers Vlad Stolyarov and Vlad Stolyarov said. "These groups specialize in breaching a target in order to open the doors — or the Windows — to the malicious actor with the highest bid."
Exotic Lily, first spotted in September 2021, is said to have been involved in data exfiltration and deployment of the human-operated Conti and Diavol ransomware strains, both of which share overlaps with the Russian cybercriminal syndicate called Wizard Spider that's also known for operating TrickBot, BazarBackdoor, and Anchor.
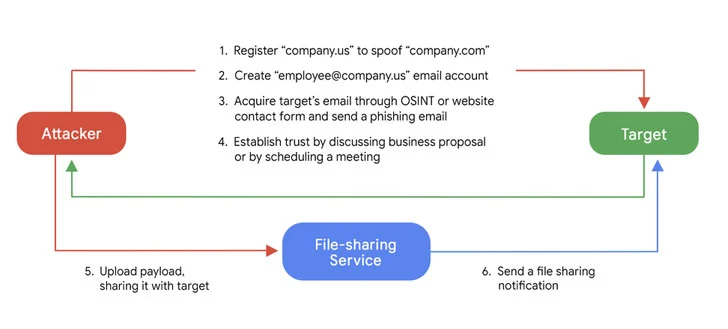
The threat actor's social engineering lures, sent from spoofed email accounts, have specifically singled out IT, cybersecurity, and healthcare sectors, although post November 2021, the attacks have grown to be more indiscriminate, targeting a wide variety of organizations and industries.
Besides using fictitious companies and identities as a means to build trust with the targeted entities, Exotic Lily has leveraged legitimate file-sharing services like WeTransfer, TransferNow and OneDrive to deliver BazarBackdoor payloads in a bid to evade detection mechanisms.
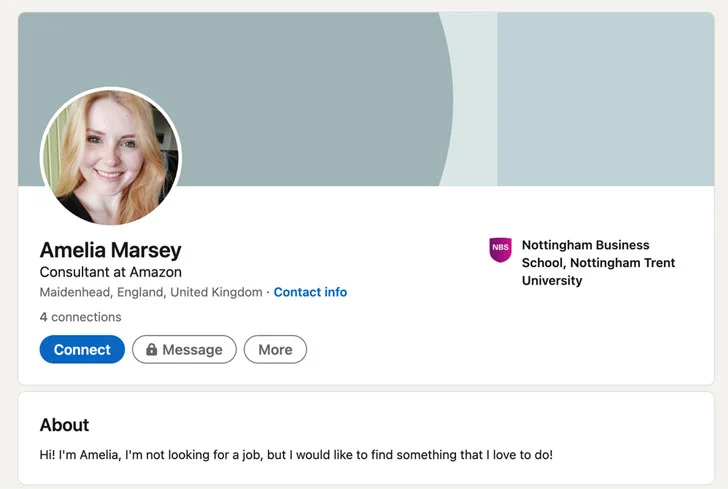
The rogue personas often posed as employees of firms such as Amazon, complete with fraudulent social media profiles on LinkedIn that featured fake AI-generated profile pictures. The group is also said to have impersonated real company employees by lifting their personal data from social media and business databases like RocketReach and CrunchBase.
"At the final stage, the attacker would upload the payload to a public file-sharing service (TransferNow, TransferXL, WeTransfer or OneDrive) and then use a built-in email notification feature to share the file with the target, allowing the final email to originate from the email address of a legitimate file-sharing service and not the attacker's email, which presents additional detection challenges," the researchers said.
Also delivered using the MHTML exploit is a custom loader called Bumblebee that's orchestrated to gather and exfiltrate system information to a remote server, which responds back commands to execute shellcode and run next-stage executables, including Cobalt Strike.
An analysis of the Exotic Lily's communication activity indicates that the threat actors have a "typical 9-to-5 job" on weekdays and may be possibly working from a Central or an Eastern Europe time zone.
"EXOTIC LILY seems to operate as a separate entity, focusing on acquiring initial access through email campaigns, with follow-up activities that include deployment of Conti and Diavol ransomware, which are performed by a different set of actors," the researchers concluded.
Source: https://thehackernews.com/2022/03/google-uncovers-initial-access-broker.html
Sign up for the e-mail list to be informed about the developments in the cyber world and to be informed about the weekly newsletter.